A critical authentication bypass in Cisco Catalyst SD-WAN Controller (CVE-2026-20182, CVSS 10.0) has entered active exploitation. The vulnerability undermines one of the fundamental promises of SD-WAN deployment: secure, managed network segmentation. For infrastructure operators running hybrid or multi-datacenter environments, this represents an immediate and serious threat.
The Peering Authentication Flaw
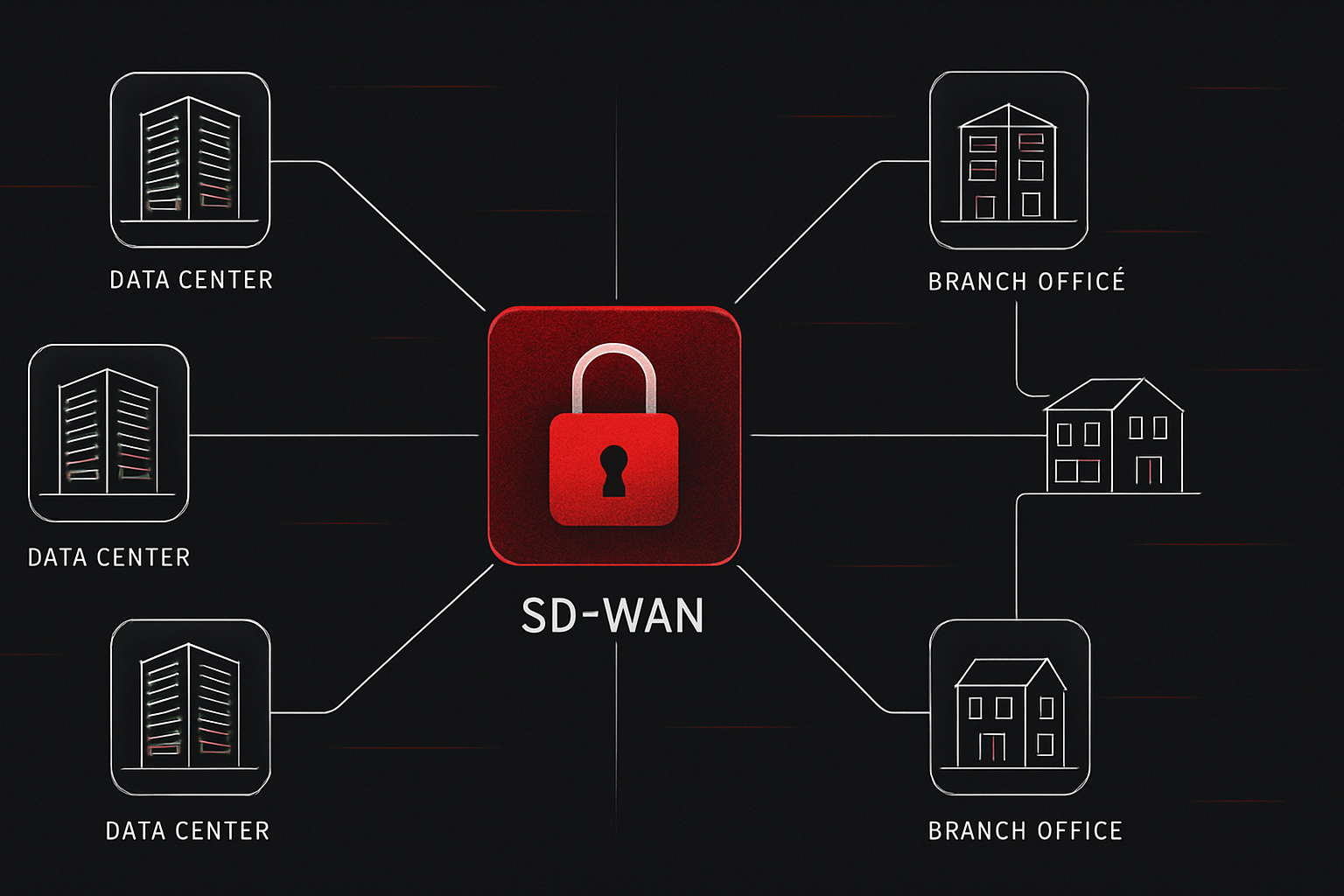
The vulnerability exists in the peering authentication mechanism of Catalyst SD-WAN Controller (formerly vSmart) and Catalyst SD-WAN Manager. An attacker can bypass authentication and obtain administrative access without valid credentials. The flaw is particularly dangerous because SD-WAN controllers sit at a critical juncture in enterprise networks—they manage traffic policies, encryption keys, and routing rules across distributed sites.
That this is being actively exploited in limited attacks, according to Cisco's advisory, suggests threat actors have already weaponized proof-of-concept code. The window between public disclosure and widespread adoption of the exploit is typically measured in hours or days, not weeks.
Why This Breaks Network Trust Models
SD-WAN is often deployed specifically to enforce zero-trust principles and reduce reliance on perimeter security. Controllers act as the policy enforcement point—they decide which traffic flows between sites, which applications get prioritised, and where encryption is applied. An attacker with controller admin access can:
- Modify traffic policies to redirect sensitive flows to attacker-controlled infrastructure
- Disable encryption on specific traffic flows
- Insert themselves as a man-in-the-middle between sites
- Access management credentials for downstream network devices
- Reconfigure VPN tunnels to intercept or monitor communication
The impact scales with deployment size. A small business loses sight of a few branch locations; an enterprise with hundreds of remote sites faces a wholesale compromise of network visibility and control.
Immediate Actions for Operators
Infrastructure providers and enterprises running Catalyst SD-WAN must patch immediately. Cisco has released updates for both vSmart Controller and SD-WAN Manager. There is no workaround for this class of flaw—authentication bypass cannot be mitigated through firewall rules or network segmentation alone.
Before patching, consider:
- Audit controller access logs. Look for API calls or administrative changes during the window when you may have been vulnerable. Many organisations will not have fine-grained logging enabled on controllers, making forensic investigation difficult.
- Check for unexpected tunnel or policy changes. Controllers track configuration history; review recent modifications for anything unauthorised.
- Isolate controllers during the patch window. If immediate patching is not possible, restrict network access to the controller to known administrative subnets only. This does not fix the vulnerability but reduces the attack surface.
- Schedule maintenance carefully. Patching an SD-WAN controller typically requires careful sequencing to avoid service disruption; plan for a maintenance window that accounts for failover and testing.
Broader Pattern in Infrastructure Security
This incident reflects a wider trend: as infrastructure becomes more abstracted and centralised—via controllers, management planes, and orchestration platforms—the security of those control systems becomes critical path. A flaw in a single piece of management software can compromise hundreds or thousands of sites simultaneously.
This is why infrastructure operators should apply defence-in-depth principles to management systems themselves: run controllers on isolated networks, restrict administrative API access by source IP, use strong authentication (certificate-based, not shared secrets), and maintain comprehensive audit logs. Many organisations still treat management networks as lower-risk than production networks, a dangerous assumption when a single compromised controller can manipulate all downstream systems.
Patch this flaw as though it were a root-cause compromise of your infrastructure. Because, in the worst case, it could be.